Before a hacker touches your network, they already know a lot about you.
Trust the process: an attacker does all the OSINT, Social Media Intelligence, Human Intelligence and social engineering searches they need to. And it’s not only about you, it’s your close friends, your employees, your vendors, your cloud stack, your VPN portal.
Sometimes even the exact person who approves invoices on Fridays.
None of that comes from hacking.
It comes from exposure. Your digital footprints scattered across the internet like breadcrumbs nobody remembers dropping.
I’ve watched companies expose themselves without realizing it, really: spend enough time around hackers and you start seeing patterns. Not just technical ones, it’s the human ones that matter.
Just open your LinkedIn feed: someone announces a new partnership, tags partner and related people (generally CEO).
Another employee proudly posts a photo from the office with internal dashboards visible on a screen behind them.
A developer pushes a GitHub repo mentioning internal tools.
A job posting reveals the exact cloud infrastructure the company runs.
Each piece on its own looks harmless.
Put them together and suddenly you have something powerful: context.
And context is the raw material of modern phishing.
Ok, lemme show you – that’s a fake one, just to get into the.. context!
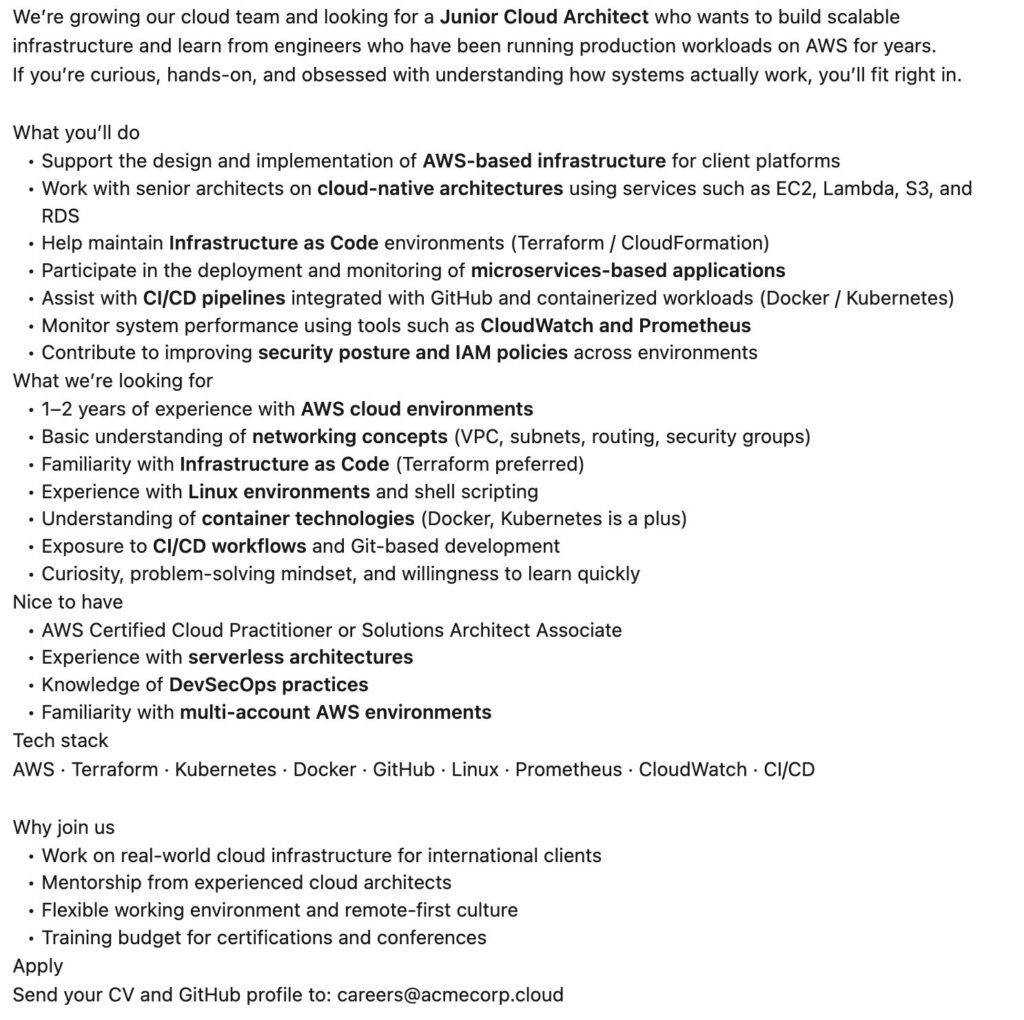
From a hacker’s perspective, a posting like this leaks quite a bit:
- Cloud provider: AWS
- Infra-as-Code: Terraform
- CI/CD tooling: GitHub
- Monitoring stack: Prometheus + CloudWatch
- Architecture style: microservices + Kubernetes
- Security model: IAM-driven
That’s gold for crafting believable phishing lures like:
- “Your Terraform pipeline failed validation”
- “GitHub Actions security alert”
- “AWS IAM policy update required”
The strange twist of cybersecurity is that sometimes the most valuable reconnaissance tool isn’t a scanner.. it’s a careers page quietly explaining how your infrastructure works to the entire inter
Basically you can understand that phishing does not start when the message arrives.
That’s the movie version, in reality the email is the final step.
Google alone can tell a surprising story about an organization.
Within an hour you can often understand how a company operates, just by googling it out. Not perfectly, but perfectly enough to impersonate it.
That’s the trick.
Security tools rarely see this layer, as most companies spend serious money on technical defenses (like firewalls, endpoint protection and very expensie threat detection platforms).
All necessary – and I mean all of them.
An attacker doesn’t search for your endpoint, at first. when they profiles a company for a phishing campaign, they’re not searching for credibility.
And they want to know:
- what services your company uses
- how your internal communication sounds
- which employees are most likely to respond
- what kind of request would feel normal
Once they have that context, the phishing email almost writes itself.
And, if we take the fake job post example before, here you are:
- “Your AWS password expired.”
- “New VPN configuration required.”
- “Amazon Service Cloud Invoice approval needed today.”
None of these messages look suspicious if they match your environment.
They look routine.
And routine is incredibly powerful.
Enough.
Fairly enough, right?

Chief Marketing Officer • social engineer OSINT/SOC/HUMINT • cyberculture • security analyst • polymath • COBOL programmer • nerd • retrogamer

